A new phenomenon stand out in recent years: security must pervade the entire software development lifecycle. Except it isn’t. Current generation of processes and tools is lacking crucial features to properly manage modern security risks. Think of the Log4J event. Were you able to identify all affected components? Were they internally developed, or you need a vendor support? How fast you were able to deliver a fix? In this talk we’ll explore the challenges, what you can do with current tools, and which gaps should be addressed by communities through better practices and new tools.
Related
What separates the highly-skilled developer from the one fresh out of college? Why is it that some developer’s code is far easier to maintain and others are nearly impossible to decipher? Both boil down fundamentally to whether you can easily understand the ideas and intent conveyed in their code. So what makes for easily understood code? There are some communication principles we can apply to our code to make it cheaper to change, and faster to understand. After all Code is read more often than it is written. It ought to be easy to read!
Episode
This post is similar to another I recently wrote on using Branch Protection Rules in GitHub. Instead of focusing on GitHub, we’ll be looking at how you can use Branch Policies in Azure DevOps (specifically, Azure Repos). If you’re using Azure Repos, but not using Branch Policies - I’d encourage you to start using them! I hope this post helps you learn how!
Blog
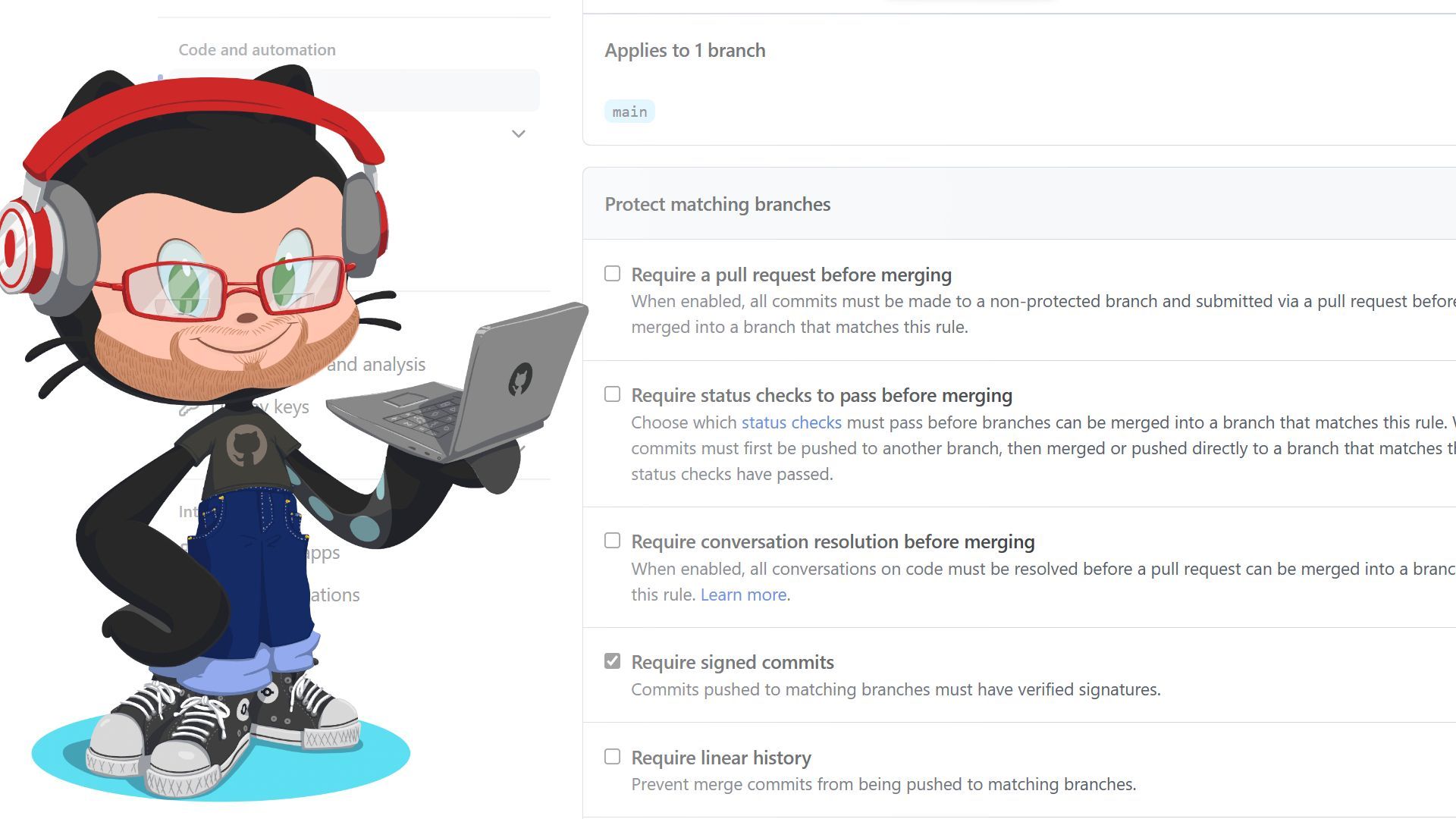
If you’re using GitHub as your source control provider, then I’d encourage you to using Branch Protection Rules if you’re not already doing so! In this blog post, we’ll cover what Branch Protection Rules are and how they can increase your code quality.
Blog
In this session, Chris is joined by DeveloperSteve Coochin, a Developer Advocate at Snyk. In this episode, Chris and Steve talk about vulns in the wild for a bit (well and to geek out in general), especially on the back of some research that Steve did recently on the likes of PHP. Steve has recently been looking into the security vulns that get let in without developers even knowing (Teaser: He was really surprised at some of them!)
Episode